Cloud Security
AIHPC supercomputer system cloud platform is a critical infrastructure for industrial AI research and development and cloud services. Users can transfer security and compliance risks through a rock-solid telecom-grade cybersecurity infrastructure and diversified integrated services to improve confidentiality, integrity and availability.
Member CenterTaizhi Cloud AI CloudBoth the platform and HPC login use two-stage two-factor authentication.Safety and complianceThis is to prevent user accounts from being stolen.
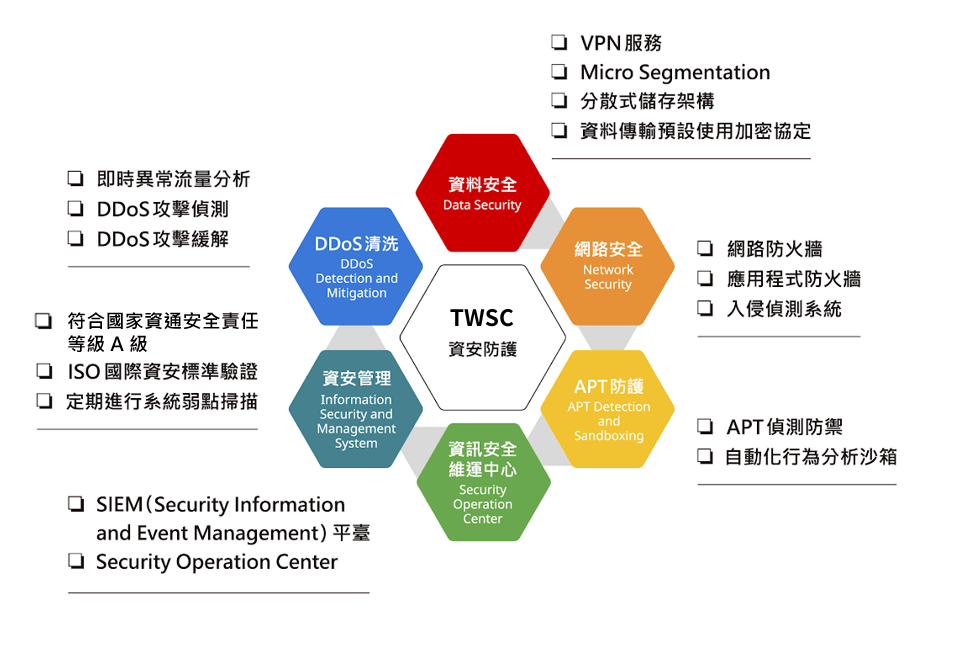
Cybersecurity protection services
Taiwan Smart Cloud provides a multi-layered telecommunications-grade cybersecurity protection mechanism: In terms of strategic security, in addition to following the Level A operating standards for cybersecurity responsibility, it also complies with the relevant operating procedures and standards of financial and medical institutions, providing telecommunications-grade cloud security infrastructure; in terms of operational security, it has integrated security protection from the management level, physical security level to the data level, ensuring the reliability of platform services; in terms of tenant security, it can work with partners to provide comprehensive tenant cybersecurity solutions to help users protect the security of data and services.
Function
Data Security Data Security
- Micro Segmentation: Implements network segmentation for virtual hosting to prevent unauthorized data access.
- Distributed storage architecture: ensures data integrity and high availability.
- Data encryption: Enhance data security and protect sensitive data with passwords.
Cybersecurity Network Security
- Network firewall: For connections from the network layer to the application layer, a high-performance firewall performs access control and traffic management.
- Intrusion Detection System: Real-time detection and identification of network threat characteristics, detection of malware and hacker behavior to maintain platform security.
APT protection APT Detection and Sandboxing
- APT Detection and Prevention: Build an automated behavior analysis sandbox to analyze intercepted malware and detect botnets and potential APT connection activities.
- Integrate the information security operations center and send APT attack warnings.
Information Security Maintenance Center Security Operation Center
- Establish a SIEM (Security Information and Event Management) platform to collect and analyze the correlation of logs from heterogeneous devices.
- The information security maintenance center monitors network traffic and issues alerts and reports on cybersecurity incidents in response to threat behaviors.
Cybersecurity Management Information Security and Management System
- Multiple ISO international cybersecurity standard certifications: Certified in cloud security and international cybersecurity, including ISO 27701 Personal Information Management System, ISO 27001:2013 Information Security Management System, ISO 27017:2015 Cloud Service Information Security, and ISO 27018:2014 Personal Privacy Data Protection. The company also continuously strengthens its internal cybersecurity controls annually to help users establish a secure and controllable environment.
- It meets the requirements of the Information and Communications Security Management Act, which classifies information and communications security responsibility level as Level A for specific non-governmental organizations.
DDoS cleaning DDoS Detection and Mitigation
- Monitor the Netflow data of external routers to analyze abnormal traffic in real time and detect potential DDoS attacks.
- We provide DDoS protection services and effectively mitigate the impact of DDoS attacks on the platform through a traffic diversion and cleaning mechanism.
AIHPC Supercomputer System – Security and Compliance
The AIHPC supercomputer system cloud platform is located in the National Network Center's server room at the National Applied Research Laboratories. The cybersecurity team possesses expertise in systems, networks, databases, programming languages, digital forensics, and massive data visualization. Under the 24-hour monitoring of the Security Operation Center (SOC), it employs a multi-layered defense concept to build an intelligent security protection mechanism. This mechanism provides various cybersecurity protection measures from the network layer access and application services, covering communication security and system security protection, and incorporating a defense-in-depth detection mechanism.
Compliance Scope
All AIHPC cloud service solutions utilize Class A IDC data center services, meeting the highest national cybersecurity standards. They have also received ISO 27017 cloud service information security and ISO 27018 personal data protection certifications, representing mainstream international standards for cloud security and providing enterprise customers with greater peace of mind when using AIHPC cloud services. Furthermore, AIHPC adheres to international and European/American standards in energy management, personal data protection, and service processes. It is also a representative of high-quality standards in Taiwan, having achieved DCOS® (Data Centre Operations Standard) Level-4 audit and verification. This ensures users receive trustworthy data center management, service levels, and secure maintenance services, and is supported by high-quality Service-Level Agreements (SLAs).
worldwide







Taiwan
other countries